Last year, the total number of mobile app downloads worldwide was calculated to be 178.1 billion.
And that number is only expected to go up this year, as more and more apps continue to show up on the market and draw our attention.
In fact, with over 5.8 million apps available to download today, you’ve probably had a lot of conversations about that amazing thing you can do on your phone because of a new app.
But have you discussed the safety of those apps you’ve been downloading, and whether or not the data on your phone is still secure?
“Using Apps Safely” might sound like a boring topic—I mean, come on, who cares about that when they’re busy taking a quiz to find out which Disney princess they are—but it’s extremely important for every user to be aware of and informed about the potential dangers of some of the apps on today’s market.
Every new app should pass certain criteria before being downloaded. And there is a huge reason why.

Apps Cultivate Data
App safety isn’t exactly a new discussion topic, but it’s one that isn’t always taken seriously. Today’s apps are new and exciting and full of promises. You can do practically anything with one—from important things like locking your front door…
…to really important things like proving you’re a true Game of Thrones fan with a Hodor keyboard (really).
But with every app you use, it cultivates more data.
What’s more, mobile marketing is making a bigger appearance because businesses are fully aware of the monetary potential that apps now carry. And this means that the data we cultivate while using our various apps is becoming more and more desirable.
How much data do we cultivate while using apps?
Think about it: We live with our phones connected to our hands; we communicate with friends and coworkers, we answer emails, we track our health, we calculate our caloric input, we shop for clothes, we keep tabs on our bank accounts… we even let our devices memorize our faces.
Just last year, Statista calculated that app users spent 77% of their valuable time on their three most-frequented apps.
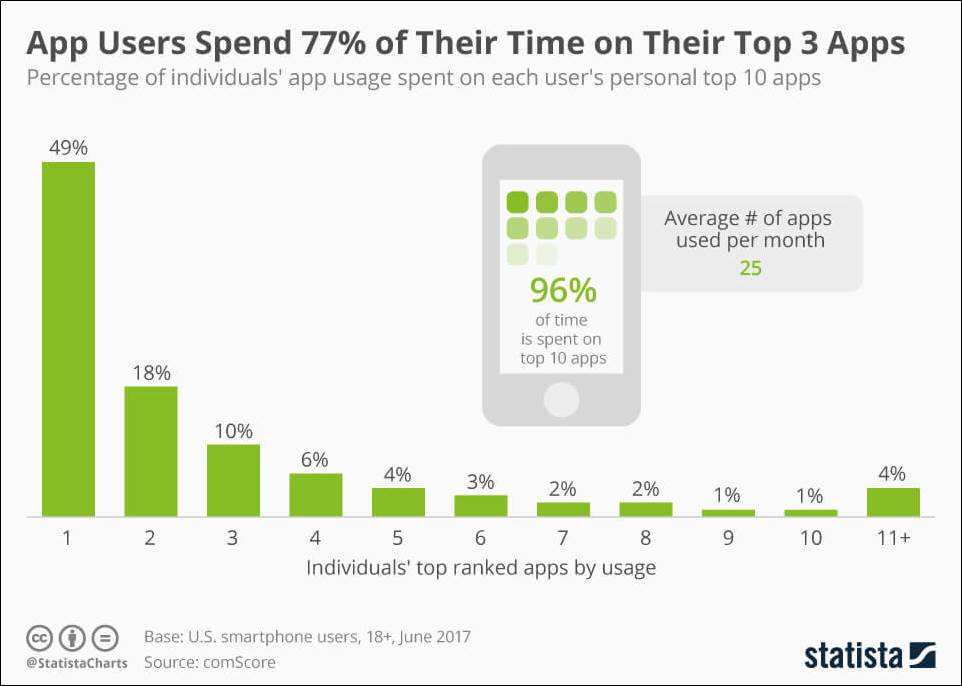
That’s a lot of time spent on apps, and a lot of data created while using them. For marketers, it means a gold mine of monetary potential.

Using Apps = Making Money
As we open our various apps, make in-app purchases, and tap on one link after another, some companies are tracking our behavior because it gives them a better picture of who we are and what motivates us to click “buy.”
This is why we have to pay attention to the integrity of every app we download. Some companies are sneaky about the data they collect and how they handle the data that they collect. It’s valuable stuff, and there’s a lot of it, so they’ve figured out an easy way to get what they want without you catching on—which is through their apps.
And that, of course, means our data privacy concerns need to extend into the world of apps.
So if we know the potential danger of downloading an untrustworthy app, then why are so many everyday users careless about which ones they download?
I mean, you wouldn’t let just anybody into your house to rifle through your closet, read your mail, browse through your personal journals, and then use that information to make money, right? So why would you allow an app to essentially do the same thing to the data on your phone?
The answer to that is this: the ease and excitement of downloading a new app far outweigh any potential threats that the app might pose.
Because of this, many of us tap the download button without giving a second thought to the app’s safety and then suffer the consequences of having downloaded a “Trojan” app—one that hides a brutal invasion.
Suddenly, we go from operating our phone to holding a data-laden device in our hands that’s being operated by hackers.
But here’s the good news: you can learn to spot a potentially malicious app before it harms you.
And you can feel more confident about the safety of your apps by checking certain things before tapping that download button. It’s easy to enjoy the benefits of some of those amazing apps out there if we just learn how to perceive whether an app is safe or not.
So, before you download anything new, make sure to run that app past a few safety checkpoints to ensure that it upholds data safety practices.
It’s easy to enjoy the benefits of some of those amazing apps out there if we just learn how to perceive whether an app is safe or not.
4 Checkpoints An App Should Pass Before Downloading
Imagine it’s a Sunday afternoon, it’s raining, everyone you know is too busy for you, and even your dog doesn’t want to look at you. You’re bored—and you want to download that cool new app and figure out all the incredible stuff it does.
If you’re bored out of your mind, you might be tempted to throw caution to the wind and hit “download” without a second thought.
But before you do that, remember that you like your data better when it’s not being exploited—so take a few minutes and double-check to see if that new app can pass these 4 safety checkpoints.
Checkpoint One: The Integrity of the App’s Marketplace
Where is that app coming from? The best route to take when downloading an app is to start from a reputable market source. Read through their privacy policies and whether or not they hold their developers accountable to their strict policies (for example, here are Apple’s developer guidelines and Google’s policy for developers). Reputable marketplaces will have strict privacy policies and guidelines and have a history of expelling violators.
Checkpoint Two: The Reviews
Read the reviews. Are the ratings high, or at least reasonable? Did any reviewers mention that they downloaded the app and were invaded by malware? Or, does every single review seem positive and fake? Some app developers will hire people to leave fake reviews in order to boost their ratings. Take some time to read through a good mix of the app’s reviews and evaluate whether it seems safe or not.
Checkpoint Three: The Company
Does the company that created the app seem safe and reputable, or does it seem questionable? Go to the company’s website and read about their history, maybe find out about their team, and see if they are a legitimate company and not some clueless app tinkerer trying to throw bad apps into the mix. Trustworthy companies aren’t going to risk their business by putting out a nasty app.
Checkpoint Four: The Privacy Policy
Before ever allowing an app to take up space on your device, take the time (I know it doesn’t sound fun, but trust me, it’s worth it) to read the company’s privacy policy in order to learn exactly WHAT information they plan on acquiring and HOW they plan to use that information.
A lot of untrustworthy apps have questionable policies that fly under the radar because most people don’t want to bother with taking the time to read through its technical lingo. Don’t let this tactic get you—read through the policy and find out whether that app will be accessing data and selling it to third parties or using it in other ways for monetary gain.
Essentially, any new app you’re checking out should come packaged with a privacy policy that you can trust your data with and that is clear and honest about its intentions.
(In fact, if you want to see an example of a solid policy right now, check out the AXEL privacy policy. We’re kind of proud of it.)

Happy App-ing
There are plenty of bad apps out there that you will want to avoid, but there are also plenty of really awesome apps out there that might actually transform the way you do things in the best possible way.
It’s up to you to be aware of the benefits and dangers of today’s apps and to assess whether the one you’re about to download will protect your private data or put it at risk.
And remember: although there are some app developers out there who want to hack your data with their invasive app, there are also a large number of trustworthy developers out there who know how to combine innovative tools with strong privacy protection.
So don’t worry—you can have fun and do amazing things on your phone while also protecting your data.
