In December and January, the technology company Accellion experienced a hack to the Accellion FTA (File Transfer Appliance), a file-sharing program aimed at enterprise customers. Since then, multiple organizations have reported data breaches linked to the software, including the large law firm Jones Day. This created quite the storm for the firm and some high-profile customers like the City of Chicago. Here, we’ll go over the hack and discuss the lessons organizations should learn from the situation.
How it happened
According to a report by the cybersecurity company FireEye[1], the initial attacks occurred via a malicious SQL injection that allowed the criminals to install a web shell on Accellion servers. Then, the hackers could run malware programs at will via the web shell. If you remember, this is very similar to the methods employed by the group behind the infamous SolarWinds hack, covered by us here and here.
Who was behind it?
Cybersecurity experts attribute the attack to the CL0P ransomware gang[2] due to increased activity on the group’s dark website that shames organizations into paying the ransom. Analysts conclude that the victims implicated on the site line up with the known victims of this breach.
The threat actors used the Accellion FTA exploits to steal data from over 100 organizations, including the Australian Securities and Investments Commission, grocery store chain Kroger, the University of Colorado, and the Jones Day law firm. We’ll be specifically looking at the Jones Day state of affairs, as it has become a juicy story.
Jones Day
The Jones Day Law Firm is a major firm headquartered in Cleveland, Ohio, employing over 2500 attorneys and serving thousands of clients globally. In February 2021, representatives confirmed the company was one of those affected by the Accellion FTA breach. Law firms have significantly more to worry about from data breaches than, say, Kroger. This is due to the sheer amount of confidential information that passes between attorneys, legal assistants, clients, and court officials. Jones Day says its internal systems weren’t compromised, but the distinction is a bit moot, given what ended up being leaked.
The City of Chicago
The most interesting insights revealed in breach so far come from leaked correspondence between Jones Day and Chicago government officials. The City of Chicago was not a formal client of the firm, but Jones Day attorneys offered advice on many legal situations. The hackers stole over 85GB of emails, images, and documents sent between the two entities.
Neither Jones Day nor the City of Chicago paid the ransom, and these files were made available on the Dark Web. The Wikileaks-esque whistleblower website DDOSecret.com released a small portion of the haul publicly and has sent the complete data set to journalists. What has been reported on offers a fascinating look behind the political curtain of America’s third-largest city:
- The Chicago Police Department created a secret drone surveillance program using money from seized assets sold after criminal investigations[3]. The budget for the drone initiative totaled nearly $8 million. The police used it to aid in missing persons cases and anti-terrorism strategies.
- Mayor Lori Lightfoot attempted to distance herself from a campaign promise regarding police reformation[4].
- Mayor Lightfoot and Illinois Governor J.B. Pritzker clashed on COVID lockdown restrictions on indoor dining.
Clandestine drone programs aside, there haven’t been many earth-shattering bombshells. Still, it’s embarrassing for both the City of Chicago and Jones Day. Mayor Lightfoot has called into question the authenticity of the emails[5], stopping short of outright denial.
It seems unlikely that a hacker group would go through the trouble of fabricating hundreds of thousands of documents to expose what amounts to normal everyday political shenanigans, but we’ll see how it shakes out.
The lesson
Jones Day and 100+ other affected organizations could have saved themselves the public embarrassment and loss of trust if they used better data transfer solutions. The Accellion FTA was a legacy file-sharing platform left largely unsupported. However, the inertia of technological adoption resulted in massive companies leaving themselves open to a data breach. Given the resources these organizations have at their disposal, the risks of sticking with old tech are unacceptable.
It’s especially objectional for a law firm like Jones Day. Their entire business is keeping confidential legal information away from the public’s eyes. While they may have the clout to recover from this issue, smaller firms would be devastated.
The takeaway for law firms and solo practices should be; take data security very seriously! Don’t rely on outdated platforms or downright insecure solutions like email attachments to share and store documents. Vet the provider you end up going with to ensure they will support the solution for the foreseeable future and continue to provide security patches along with new privacy features. Not doing so leaves you susceptible to catastrophic scenarios.
The right choice
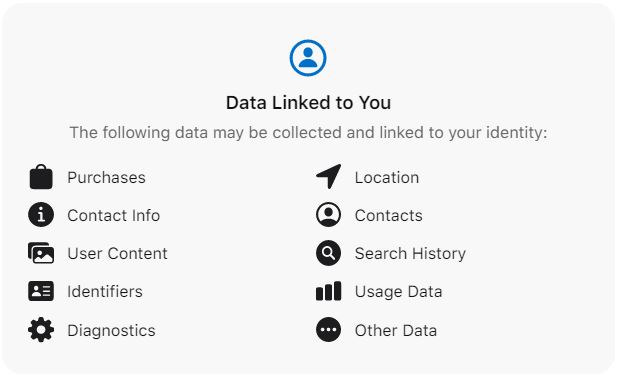
Our file-sharing and cloud storage platform AXEL Go prevents data breaches. It’s the perfect solution for those working within targeted industries such as the legal sector. Our development team built AXEL Go from a framework of security and privacy. It combines secure blockchain technology, decentralized IPFS implementation, and military-grade file encryption to keep the most sensitive files safe.
To learn more, please visit AXELGo.app and sign up for a free 14-day trial of our Premium service. You get to try out all of the innovative features, such as Secure Fetch and storage encryption. Our team is always hard at work improving the platform and releasing updates. Once you see the AXEL difference, you’ll never go back to insecure data transfer systems again.
[1] Andrew Moore, Genevieve Stark, Isif Ibrahima, Van Ta, Kimberly Goody, “Cyber Criminal Exploit Accellion FTA for Data Theft and Extortion”, FireEye.com, Feb. 22, 2021, https://www.fireeye.com/blog/threat-research/2021/02/accellion-fta-exploited-for-data-theft-and-extortion.html
[2] Tara Seals, “Accellion FTA Zero-Day Attacks Show Ties to Clop Ransomware, FIN11”, ThreatPost.com, Feb. 22, 2021, https://threatpost.com/accellion-zero-day-attacks-clop-ransomware-fin11/164150/
[3] Tom Schuba, Frank Main, “CPD launched secret drone program with off-the-books cash”, Chicago Sun Times, May 12, 2021, https://chicago.suntimes.com/city-hall/2021/5/11/22425299/cpd-chicago-police-drone-secret-emails-hack-lori-lightfoot-dodsecrets-city-hall
[4] Gregory Pratt, “Computer hackers stole thousands of Lightfoot administration emails. Here’s a look at some of what they leaked online.”, Chicago Tribune, May 14, 2021, https://www.chicagotribune.com/politics/ct-lightfoot-administration-hacked-emails-closer-look-20210514-havyv352lfegrklmfi76a25wfi-story.html
[5] Bernie Tafoya, “Lightfoot questions legitimacy of city emails made public after hack”, WBBM NewsRadio 780 AM, May 11, 2021, https://www.audacy.com/wbbm780/news/local/mayor-questions-legitimacy-of-emails-made-public-after-hack