Barely two months after the massive SolarWinds attack (that experts are still attempting to unravel) comes news of perhaps an even larger successful attack. In a patch release on March 2nd, Microsoft announced they fixed four critical vulnerabilities to their Exchange Server email system. No big deal, right? Well, buckle up.
The scope
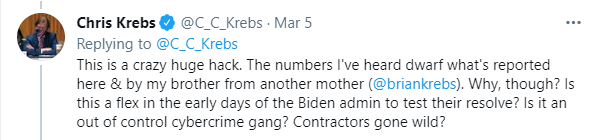
As it turns out, hackers exploited these zero-day (previously unknown) vulnerabilities for at least two months before Microsoft released the security patch. The security holes themselves were present for over ten years, so it may be an even more widespread issue. During the last two months, however, it seems as if over 30,000 organizations running Exchange Server were compromised in the United States alone[1]. Worldwide, the number grows to hundreds of thousands of likely victims. And that could be a lowball estimate! According to former CISA Director Chris Krebs, “The numbers I’ve heard dwarf what’s reported here,” referring to a report indicating the 30K number. That’s staggering!
The situation
In early January, the red team ethical hacking group, DEVCORE, led by the Orange Tsai, first reported two of the four zero-day vulnerabilities to Microsoft[2]. Soon after, the cybersecurity firm Volexity detected actual attacks from then-unknown entities using the exploits[3]. By late January, analysts mapped out the breaches and deciphered some details.
The threat actors were installing backend “web shells” on the Exchange servers. Web shells are malicious code injected into web applications that can give hackers administrator access to the infected servers. Then, the cybercriminals can run commands at-will. In this case, it appears that the hackers stole private emails and primed the networks for other malicious activity. Some analysts worry that the affected systems may be vulnerable to future ransomware attacks[4].
The victims
The unfortunate truth is that nearly any organization running non-cloud-based Microsoft Exchange email servers could be a victim. As awareness of the hack spreads, the tally of compromised organizations grows. The scope of the attack is unprecedented. In an official statement, Microsoft claimed that the group responsible for the attack typically targets “infectious disease researchers, law firms, higher education institutions, defense contractors, policy think tanks, and NGOs,[5]” but this attack appears much less selective.
According to the cybersecurity firm Huntress, many of the clients they confirmed as having the web shell installed do not it into these categories[6]. As the Senior Security Researcher of the company says, “These companies do not perfectly align with Microsoft’s guidance as some personas are small hotels, an ice cream company, a kitchen appliance manufacture, multiple senior citizen communities and other ‘less than sexy’ mid-market businesses.”
There have been some high-profile organizations already disclosing breaches, though:
- European Banking Authority. On March 7th, the EBA, which has a supervisory role in the European Union’s banking industry, admitted hackers compromised their Exchange email servers[7]. Luckily, a security analysis turned up no evidence that the cybercriminals stole any data.
- Norway’s parliament. The Norwegian parliament, the Storting, did not get off so easy. With the digital forensic investigation still underway, the governmental body admitted, “We know that data has been extracted, but we do not yet have a full overview of the situation.[8]” This is the second major breach the Storting experienced over the past three months.
Undoubtedly, the list of known organizations affected by the situation will increase significantly in the upcoming days.
The perpetrators
Microsoft has consistently assigned blame to a Chinese state-sponsored hacking group dubbed ‘HAFNIUM.[9]’ Details for this assessment are scarce. Evidently, the behavior and tactics are similar to known Advanced Persistent Threats (APTs) from China. The group also worked through leased VPN servers located in the United States, which may point toward a Chinese origin.
However, after the initial disclosure, cybersecurity firms reported that other APTs have joined in on the illicit fun. According to a report by the cybersecurity company ESET, at least ten other APTs are exploiting the Exchange flaws[10]. This includes Tick, LuckyMouse, Calypso,Websiic, Winnti Group, Tonto Team, Cobalt Group, Mikroceen, and three unknown groups. It’s unclear if there is any proper coordination between these factions. The majority -but not all- of them share connections to China, but the fact that multiple web shells were present on some of the affected servers indicates a lack of collaboration.
As was mentioned in our previous SolarWinds article, attribution of an attack is quite tricky. There are instances of APTs disguising their activity and successfully pinning it on a different country. And, as the Vault 7 Wikileaks dump proved, nations have sophisticated tools that obfuscate the attackers’ true origins[11]. However, with so many Chinese APTs linked to the situation, it becomes more challenging to deny involvement (unsurprisingly, the Chinese Communist Party has denied the allegations.)
Uncertainty
So, where do we go from here? As mentioned, Microsoft released a patch that fixed the vulnerabilities. If your organization runs an Exchange email server, install the patches immediately. Microsoft says that these fixes will not help systems already infiltrated with web shells. If you suspect an infection, have cybersecurity professionals analyze the network.
Other than that, there isn’t too much you can do. Experts are still evaluating the full extent of the attack, and nobody knows if/when further damage, such as ransomware, will occur. The situation’s historic magnitude makes it especially scary because it goes against the traditionally-cautious cyber strategy of China’s APTs. It’s brazen and impossible to ignore. What will the fallout be? Only time will tell.
Data security for all
Are you doing enough to protect your files from hackers and intruders? If you’re using a Big Tech solution for file-sharing and online storage, the answer is ‘no.’ Get serious about data security and use the private, safe file-sharing and storage platform AXEL Go. It utilizes blockchain technology, the InterPlanetary File System (IPFS), and robust password encryption to keep your documents out of reach from data mining corporations and hackers. Download it today for Windows, OSX, Android, or iOS and experience a better way to share.
[1] Brian Krebs, “At Least 30,000 U.S. Organizations Newly Hacked Via Holes in Microsoft’s Email Software”, Krebsonsecurity.com, March 5, 2021, https://krebsonsecurity.com/2021/03/at-least-30000-u-s-organizations-newly-hacked-via-holes-in-microsofts-email-software/
[2] “What is ProxyLogon”, Proxylogon.com, March 2021, https://proxylogon.com/#timeline
[3] Josh Grunzweig, Mathew Meltzer, Sean Koessel, Steven Adair, Thomas Lancaster, “Operation Exchange Marauder: Active Exploitation of Multiple Zero-Day Microsoft Exchange vulnerabilities.
[4] Brian Krebs, “Warning the World of a Ticking Time Bomb”, Krebsonsecurity.com, March 9, 2021, https://krebsonsecurity.com/2021/03/warning-the-world-of-a-ticking-time-bomb/
[5] “HAFNIUM targeting Exchange Servers with 0-day exploits”, Microsoft.com, March 2, 2021, https://www.microsoft.com/security/blog/2021/03/02/hafnium-targeting-exchange-servers/
[6] John Hammond, “Rapid Response: Mass Exploitation of On-Prem Exchange Servers”, March 3, 2021, https://www.huntress.com/blog/rapid-response-mass-exploitation-of-on-prem-exchange-servers
[7] Davey Winder, “EU Banking Authority Hacked As Microsoft Exchange Attacks Continue”, March 9, 2021, https://www.forbes.com/sites/daveywinder/2021/03/09/eu-banking-authority-hacked-as-microsoft-exchange-attacks-continue/?sh=29f2026d2fe0
[8] Richard Speed, “A nei! Noway’s Stortinget struck by Microsoft Exchange malware”, The Register, March 11, 2021, https://www.theregister.com/2021/03/11/stortinget_attack/
[9] “HAFNIUM targeting Exchange Servers with 0-day exploits”, Microsoft.com, March 2, 2021, https://www.microsoft.com/security/blog/2021/03/02/hafnium-targeting-exchange-servers/
[10] Matthieu Faou, Mathieu Tartare, Thomas Dupuy, “Exchange servers under siege from at least 10 APT groups”, March 10, 2021, https://www.welivesecurity.com/2021/03/10/exchange-servers-under-siege-10-apt-groups/
[11] “Vault 7: CIA Hacking Tools Revealed”, Wikileaks.org, March 7, 2017, https://wikileaks.org/ciav7p1/index.html